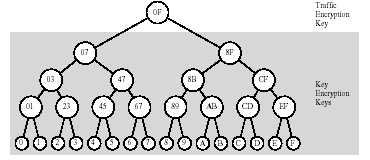
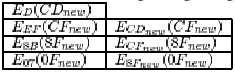
Assume C is leaving. This means that the keys it knew (Key Encryption Keys CD, CF, 8F, and the Traffic Encryption Key 0F) need to be viewed as compromised and have to be changed in such a way that C cannot acquire the new keys. This is done efficiently by following the tree from the leaf node corresponding to the leaving participant to the TEK stored in the root node, and encrypting the new node keys with all appropriate underlying node or leaf keys. For our example, the tree in the above-left figure shows that the new Key Encryption Key CDnew (replacement for CD) needs to be received by D, CFnew by participants D, E and F, 8Fnew by 8...B, D...F , and the new Traffic Encryption Key 0Fnew by every participant except C. Instead of encrypting the new keys individually for each of the intended participants, we take advantage of the existing hierarchy:
- CDnew is encrypted for D, the only recipient in need of it.
- CFnew is sent twice, each copy encrypted with one of its two children keys, the existing EF and the new CDnew, so it can be decrypted by the intended recipients D...F .
- 8Fnew is similarly encrypted for those knowing 8B or CFnew.
- 0Fnew is finally encrypted for those holding key 07 or key 8Fnew.